This blog series will explain the process of hacking SAP password hashes: also know as SAP password hacking. The process of hacking will be explained and appropriate countermeasures will be explained.
In this third blog we will continue with more complex attacks on the SAP password hashes and will also explain more preventive measures. Now we focus on the SAP PWDSALTEDHASH hash.
For the first blog on attacking the SAP BCODE hash click here.
For the second blog on attacking the SAP PASSCODE has click here.
For follow up blog on improving attack speed by applying rule-based attack, click here. And the blog on optimizing the attack. And the blog on extended word lists.
Questions that will be answered in this blog are:
- How to get the PWDSALTEDHASH codes?
- How does the dictionary attack work?
- How does the dictionary combination attack work?
- How does the dictionary with mask attack work?
- What more can I do to prevent a password attack?
Getting the PWDSALTEDHASH codes
The testusers 1 to 5 have been given a new password and the security admin has done its job. This is what you see in USR02:
Double clicking on a line and scrolling down will give you the PWDSALTEDHASH field content:
Getting many is too much work. For this you can use code of the program ZFETCH_PWDSALTEDHASH below:
*&--------------------------------------------------------------------* *& Report ZFETCH_PWDSALTEDHASH *&--------------------------------------------------------------------* REPORT ZFETCH_PWDSALTEDHASH. DATA: LV_USR02 TYPE USR02. DATA: LV_STRING TYPE STRING. SELECT * FROM USR02 INTO LV_USR02 WHERE PWDSALTEDHASH NE SPACE. CONCATENATE LV_USR02-BNAME '
The output for our testusers is now:
You need to save the part from {x-issha etc in a new file. The user ID in front is not needed. It is just needed in case you decrypt a password from a hash to go find the user ID.
The dictionary attack
We still assume that there is a very strict policy on strong password:
- Minimum length 10
- Minimum 1 upper, lower, digit and special
Since the admin has cleaned up the BCODE we have no idea on the first 8 characters now.
The trick we will use is the dictionary attack. We assume some of the users will use a password with the following rule:
- Take a word
- Capitalize first letter, rest is small
- Add a digit
- Add a special character
As input file for this attack we take all word from the Webster Dictionary: webster dictionary file.
We now go back to our Hashcat directory on C:\HC and give following command:
hashcat64 -a 6 -m 10300 -p : --session=all --force -o "C:\HC\users_found.txt" --outfile-format=3 --markov-disable --remove -u 128 --gpu-temp-abort=80 --gpu-temp-retain=70 "C:\HC\pwdsaltedhash testusers.txt" "C:\HC\webster- dictionary.txt" ?d?s
Command explanation: attack mode 6 for dictionary attack and 10300 for SAP PWDALSTEDHASH format.
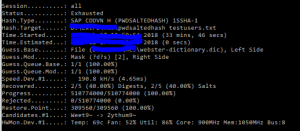
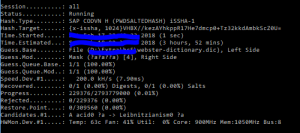
And now hashcat is showing is parallelization power:
To test all the combinations on the 5 users only 30 minutes are needed, with almost 200.000 tries per second.
2 passwords were found: TESTUSER1 with password Theobald1! and TESTUSER5 with password Tetrazotization5{.
Especially the last one is striking: this is normally not considered a simple password: Tetrazotization5{. But because it appears in a dictionary it is relative simple to retrieve.
Combination attack with dictionary
To really show the speed, we will now perform the combination attack explained in the previous blog again. We will use the dictionary in combination with the popular extension file. Command to give:
hashcat64 -a 1 -m 10300 -p : --session=all --force -o "C:\HC\testusers_found.txt" --outfile-format=3 --remove -u 128 --gpu-temp-abort=80 --gpu-temp-retain=70 "C:\HC\pwdsaltedhash testusers.txt" "C:\HC\webster- dictionary.txt" "C:\HC\Popular extensions.txt"
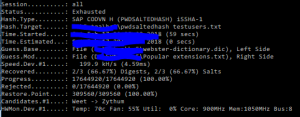
And now the performance and speed is even higher:
2 out of 3 remaining passwords were found in 1 minute only!
TESTUSER2 with Themis2018! and TESTUSER3 with Vacation123!
Dictionary with mask attack
For the last to be found password, we will use the dictionary with mask attack.
Command to give:
hashcat64 -a 6 -m 10300 -p : --session=all --force -o "C:\HC\testusers_found.txt" --outfile-format=3 --markov-disable --remove -u 128 --gpu-temp-abort=80 --gpu-temp-retain=70 "C:\HC\pwdsaltedhash testusers.txt" "C:\HC\webster- dictionary.txt" ?a?a
We try with 2 random characters after the word. After some time nothing. Then we increase to 3 characters:
hashcat64 -a 6 -m 10300 -p : --session=all --force -o "C:\HC\testusers_found.txt" --outfile-format=3 --markov-disable --remove -u 128 --gpu-temp-abort=80 --gpu-temp-retain=70 "C:\HC\pwdsaltedhash testusers.txt" "C:\HC\webster- dictionary.txt" ?a?a?a
It runs for 4 hours with about 200.000 guesses per second:
And it finally finds the last password: TESTUSER4 with Organoid1@#
Dictionaries
The example above is just one dictionary. Also think about dictionaries with names of persons, football clubs, cities and countries, etc. Largest dictionary so far is called the Wikipedia dictionary. It is about 250 MB large and contains all the unique words used on Wikipedia.
Preventive measures
Preventive measure 1: user education
Educate your users not to take a dictionary word directly and only add a digit letter.
Especially power users, like basis and user administrators, should really receive this education. Don’t assume they know. 90% of them does not, or even hands out passwords like Welcome2018!
Preventive measure 2: extra strong passwords for background and power users
You can set extra strong password requirements for background users and power users (basis and user administrators). This can be done by setting up specific security policies. This is explained in this blog.
Preventive measure 3: stronger hashes
By creating stronger hashes, the attackers need more time. It will not stop them, but slow them down. Read more on setting stronger hashes in this dedicated blog.
Next blog
The next blog will focus on rule based attack mode, which is one of the most effective methods.


Hello,
I saw your article and had to think about another article I read few days ago. Maybe you are interested: https://www.shortcut-it.com/blog/index.php?about-security-and-passwords
I am not an expert, but what I found remarkable is that the approach in this article was not to decrypt hash values. Instead, they overwrite a hash value of any user with a hash value that represents a known password. And the algorithm behind CODVN ‘H’ makes this possible, unlike older algorithms.
Kind regards,
Harald Rautemann
Hi Harald,
In the referred article they take a known password and force table update of the unknown password to the know password.
A similar hack I have described in blog about cross client hacking: http://saptechnicalguru.com/cross-client-access-hacking/
Excellent article. But I have a question, is it necessary to run the z program to get the user and the hash or can I do a select?
Select can work. As well as SE16.