In S4HANA the SSCR and developer key procedure are no longer present. This means you have to use proper authorization concept to determine which person is allowed to developer Z ABAP code and which developer is allowed to modify standard SAP ABAP code.
Questions that will be answered in this blog are:
- Why has the has the procedure been removed?
- How do I protect code adjustments from unauthorized changes?
S4HANA developer key
The title is a bit misleading. In S4HANA there are no developer keys and object keys any more.
Background of this change be SAP can be found in OSS note: 2309060 – The SSCR license key procedure is not supported in SAP S/4 HANA.
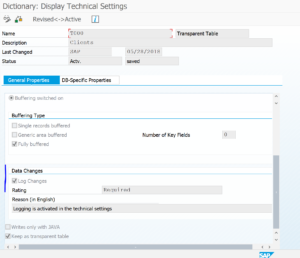
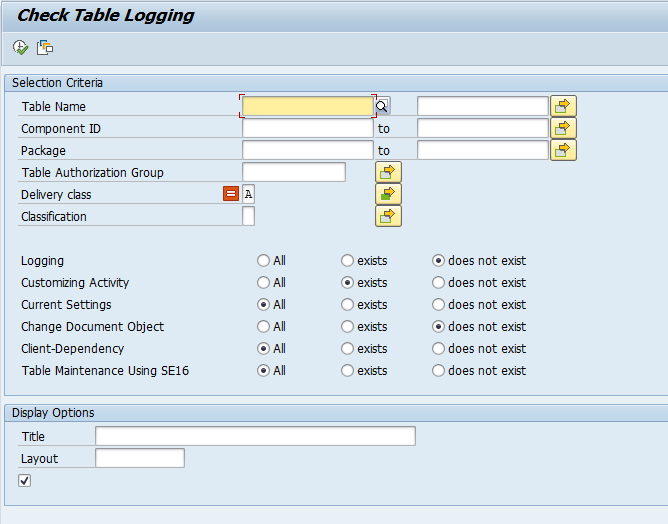
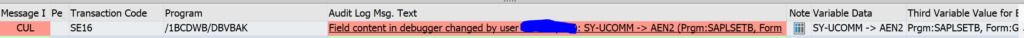
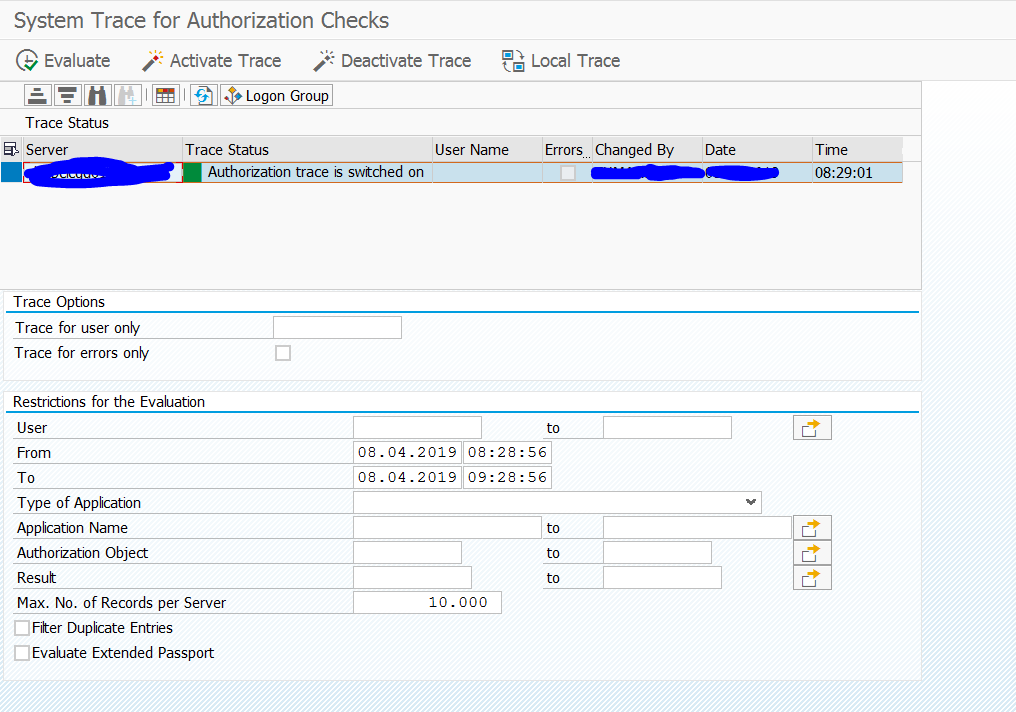
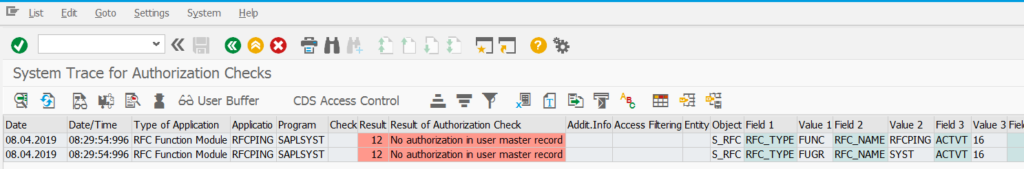
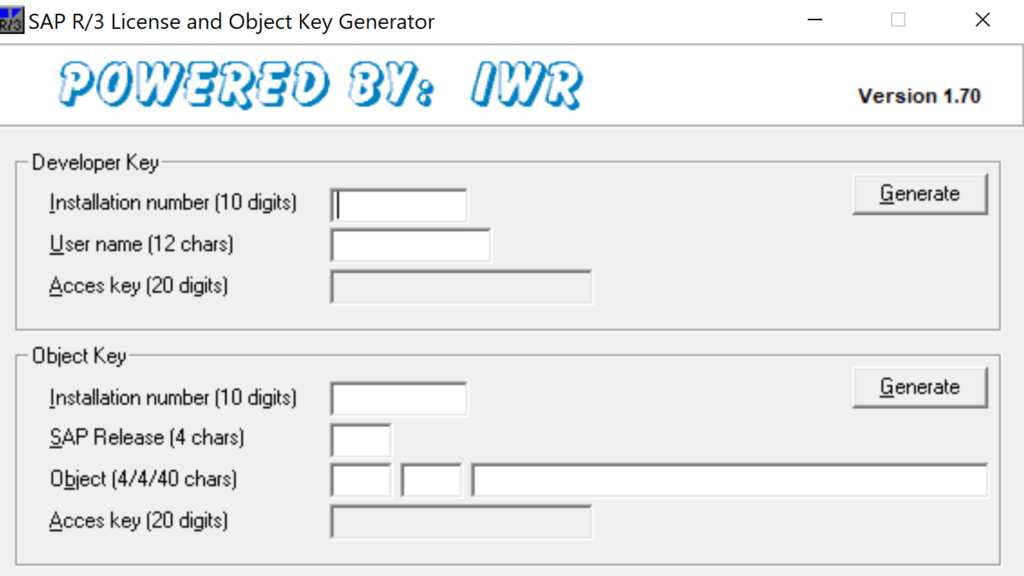
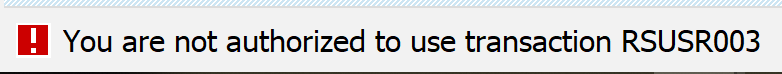
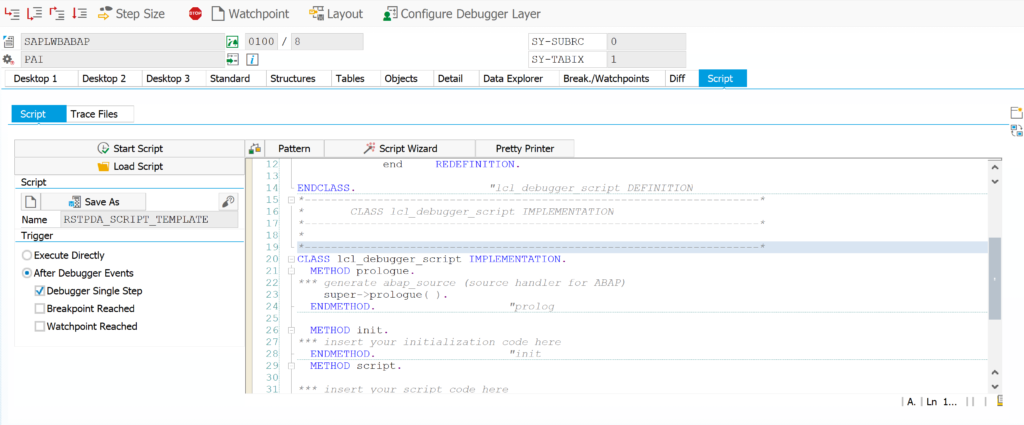
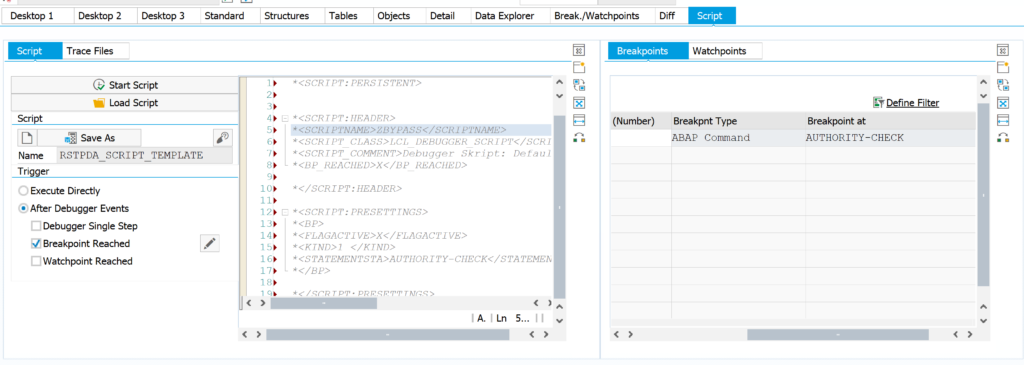
So in S4HANA, you must set up authorizations for S_DEVELOP properly. The development key and SSCR procedure are hacked anyhow (see blog).
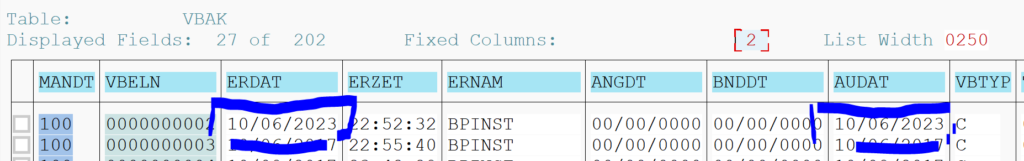
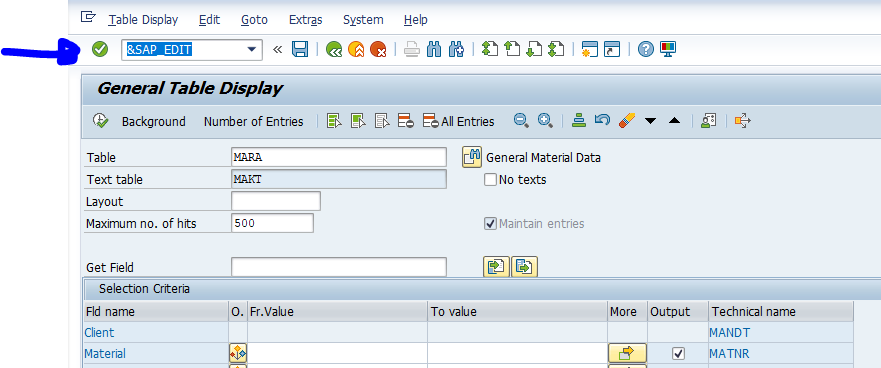
With S_DEVELOP you have to set create/change rights for the packages and or objects. For custom code only hand out Z* privileges.
If you hand out a * for the objects or classes, then the developer can also change standard SAP.
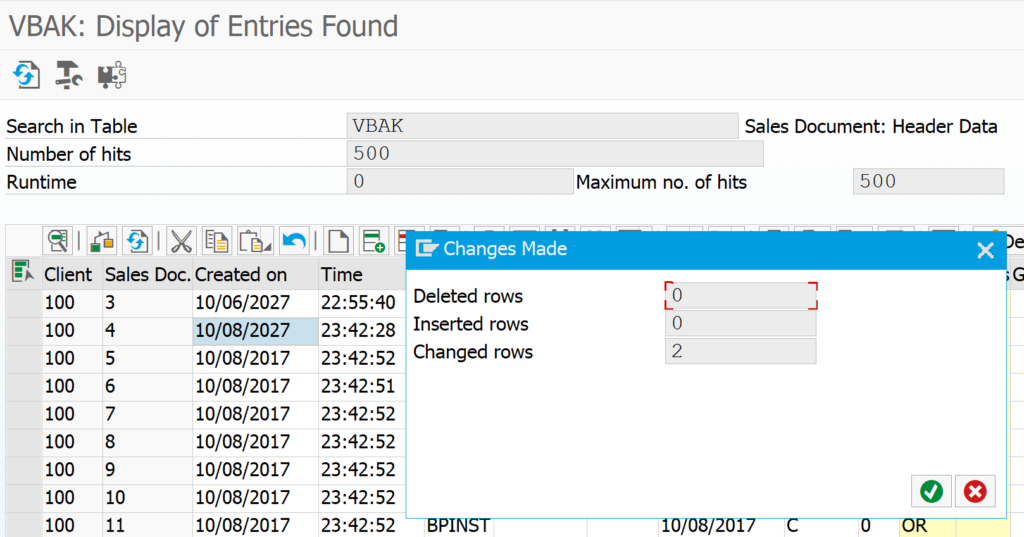
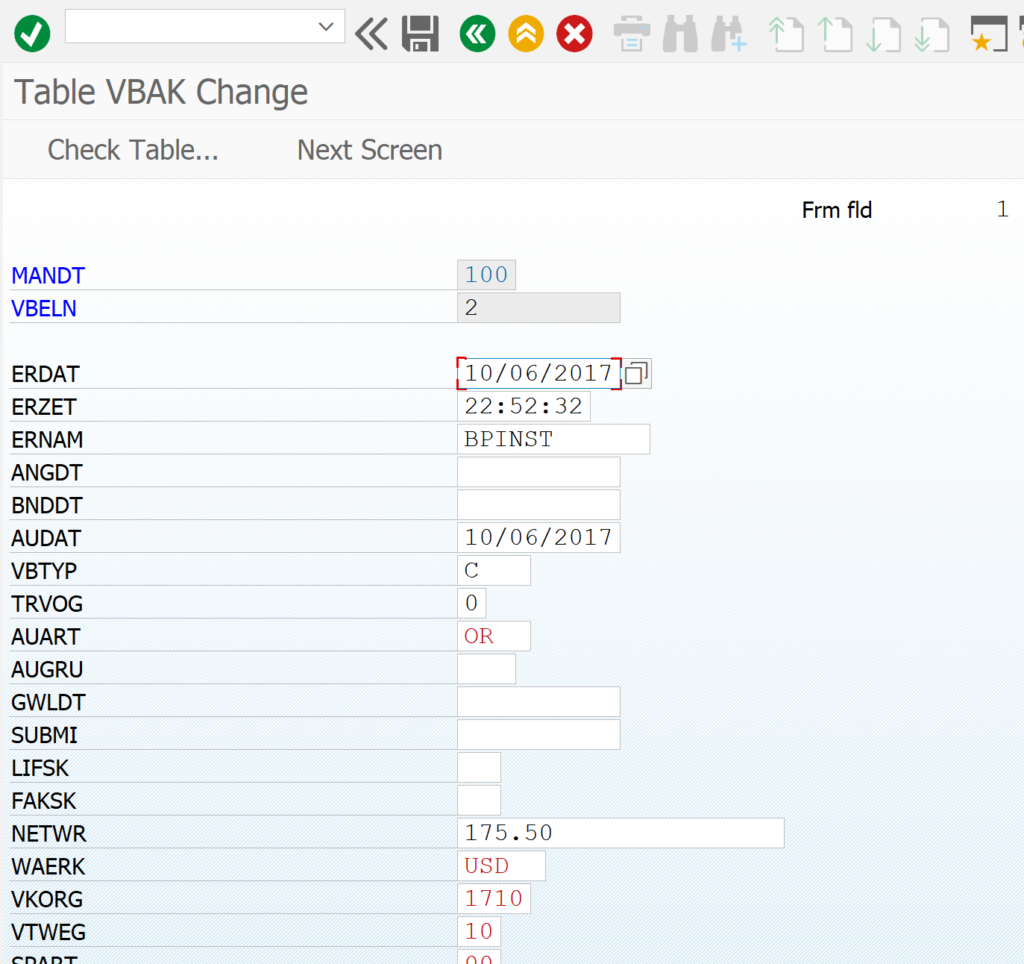
Changes to standard SAP in S4HANA
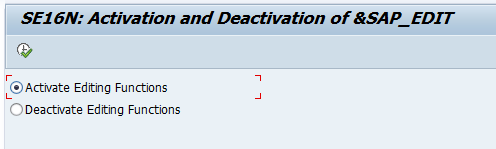
The SCCR procedure is gone in S4HANA. This means if you want to adjust standard SAP code and you have the authorizations, you can without any SSCR screen asking you for the modification key.
Again also here: i you hand out a * for the objects or classes, then the developer can also change standard SAP.
All protection of ABAP code in S4HANA is arranged via authorization.
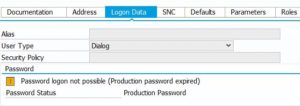
Developer license measurement in S4HANA
The move away from DEVACCESS has also made the developer license measurement in S4HANA complex. Read more in this blog.